制限なく作成可能 — 無制限のダウンロードと、強力な AI 編集機能
制限なく作成可能 — 無制限のダウンロードと、強力な AI 編集機能
新しいフィルターが追加されました
並べ替え
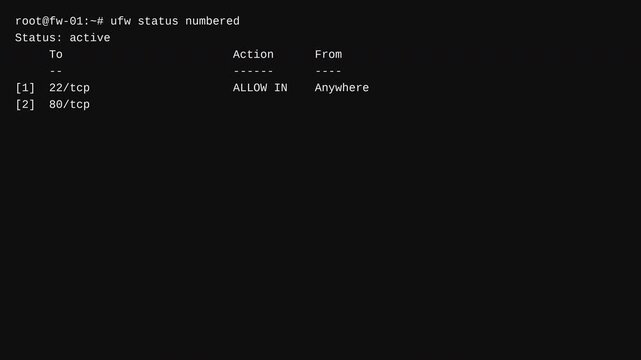
ビデオ 内の vulnerability testing の検索結果 829 件
地域を選択してください
選択した地域によって、Adobe Stock Web サイトに表示される言語やプロモーションの内容が異なる場合があります。
北米
南米
- Venezuela
- Algeria - English
- Armenia - English
- Azerbaijan - English
- Bahrain - English
- Belgium - English
- Belgique - Français
- België - Nederlands
- Česká republika
- Croatia - English
- Cyprus - English
- Danmark
- Georgia - English
- Deutschland
- Eesti
- Egypt - English
- España
- France
- Greece - English
- Iceland - English
- Ireland
欧州、中東、アフリカ
- Israel - English
- Italia
- Jordan - English
- Казахстан
- Kenya - English
- Kuwait - English
- Киргизия
- Latvija
- Lebanon - English
- Lietuva
- Luxembourg - Deutsch
- Luxembourg - English
- Luxembourg - Français
- Mauritius - English
- Moldova - English
- Hungary - English
- Malta - English
- Morocco - English
- Nederland
- Nigeria
- Norge
- Oman - English