已新增篩選器
排序方式:
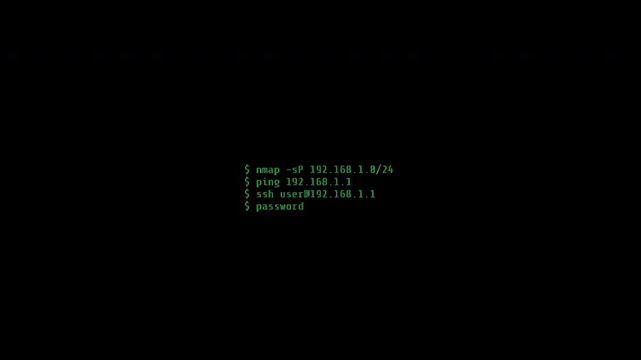
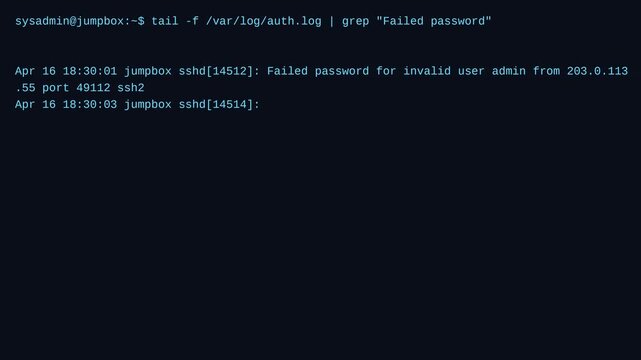
在影片中找到 216 個「ssh」的結果
選擇區域
選取區域後,Adobe Stock 網站上顯示的語言和宣傳內容可能會有所改變。
北美洲
南美洲
- Venezuela
- Algeria - English
- Armenia - English
- Azerbaijan - English
- Bahrain - English
- Belgium - English
- Belgique - Français
- België - Nederlands
- Česká republika
- Croatia - English
- Cyprus - English
- Danmark
- Georgia - English
- Deutschland
- Eesti
- Egypt - English
- España
- France
- Greece - English
- Iceland - English
- Ireland
歐洲、中東及非洲
- Israel - English
- Italia
- Jordan - English
- Казахстан
- Kenya - English
- Kuwait - English
- Киргизия
- Latvija
- Lebanon - English
- Lietuva
- Luxembourg - Deutsch
- Luxembourg - English
- Luxembourg - Français
- Mauritius - English
- Moldova - English
- Hungary - English
- Malta - English
- Morocco - English
- Nederland
- Nigeria
- Norge
- Oman - English