Prueba gratuita: obtén 10 imágenes de Stock y herramientas de edición con IA
Prueba gratuita: obtén 10 imágenes de Stock y herramientas de edición con IA
Se han añadido nuevos filtros
Ordenar por
Prueba también:
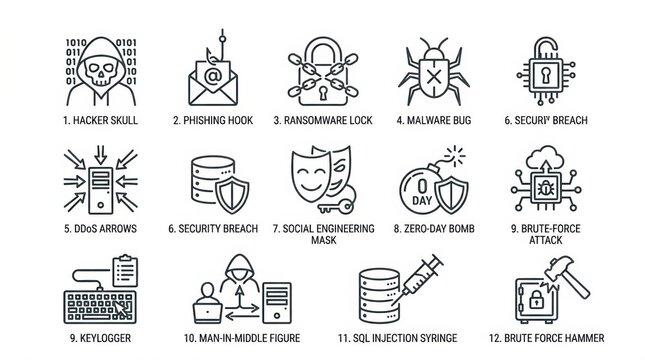
keylogger en imágenes,
keylogger en vídeos,
keylogger en Premium
Elige una región
Al seleccionar una región, podría cambiar el idioma y el contenido promocional que aparece en el sitio web de Adobe Stock.
América del Norte
América del Sur
- Venezuela
- Algeria - English
- Armenia - English
- Azerbaijan - English
- Bahrain - English
- Belgium - English
- Belgique - Français
- België - Nederlands
- Česká republika
- Croatia - English
- Cyprus - English
- Danmark
- Georgia - English
- Deutschland
- Eesti
- Egypt - English
- España
- France
- Greece - English
- Iceland - English
- Ireland
Europa, Oriente Medio y África
- Israel - English
- Italia
- Jordan - English
- Казахстан
- Kenya - English
- Kuwait - English
- Киргизия
- Latvija
- Lebanon - English
- Lietuva
- Luxembourg - Deutsch
- Luxembourg - English
- Luxembourg - Français
- Mauritius - English
- Moldova - English
- Hungary - English
- Malta - English
- Morocco - English
- Nederland
- Nigeria
- Norge
- Oman - English