Teste grátis: obtenha 10 imagens do Stock, além de ferramentas de edição com IA
Teste grátis: obtenha 10 imagens do Stock, além de ferramentas de edição com IA
Novos filtros adicionados
Classificar por
Experimente também:
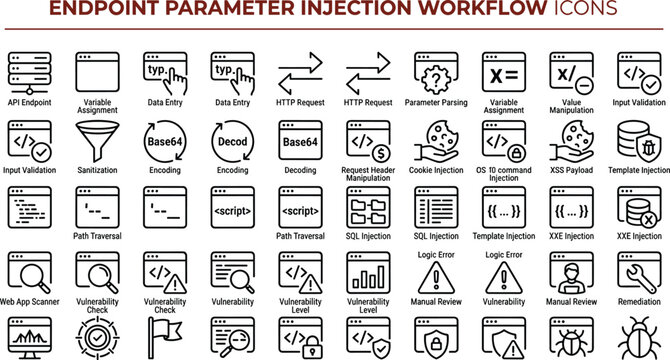
exploit em imagens,
exploit em vídeos,
exploit em modelos,
exploit em Premium
Escolher a região
A seleção de uma região pode alterar o idioma e o conteúdo promocional exibido no site do Adobe Stock.
América do Norte
América do Sul
- Venezuela
- Algeria - English
- Armenia - English
- Azerbaijan - English
- Bahrain - English
- Belgium - English
- Belgique - Français
- België - Nederlands
- Česká republika
- Croatia - English
- Cyprus - English
- Danmark
- Georgia - English
- Deutschland
- Eesti
- Egypt - English
- España
- France
- Greece - English
- Iceland - English
- Ireland
Europa, Oriente Médio e África
- Israel - English
- Italia
- Jordan - English
- Казахстан
- Kenya - English
- Kuwait - English
- Киргизия
- Latvija
- Lebanon - English
- Lietuva
- Luxembourg - Deutsch
- Luxembourg - English
- Luxembourg - Français
- Mauritius - English
- Moldova - English
- Hungary - English
- Malta - English
- Morocco - English
- Nederland
- Nigeria
- Norge
- Oman - English